A Strong Mutual Authentication Protocol for Securing Wearable Smart Textile Applications. - Document - Gale Academic OneFile

An efficient authentication and key agreement protocol for IoT-enabled devices in distributed cloud computing architecture | EURASIP Journal on Wireless Communications and Networking | Full Text
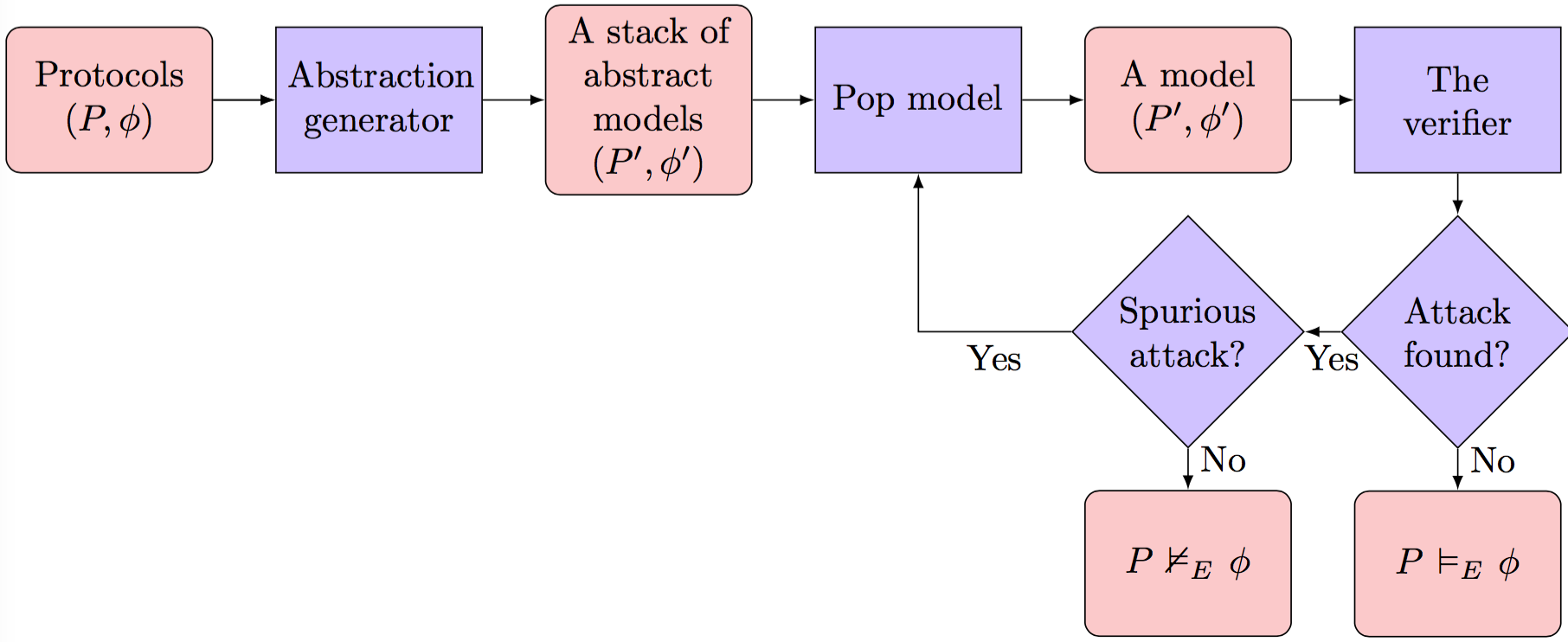
GitHub - binhnguyen1984/scyther-abstraction: The Scyther-abstraction Tool for the symbolic analysis of security protocols
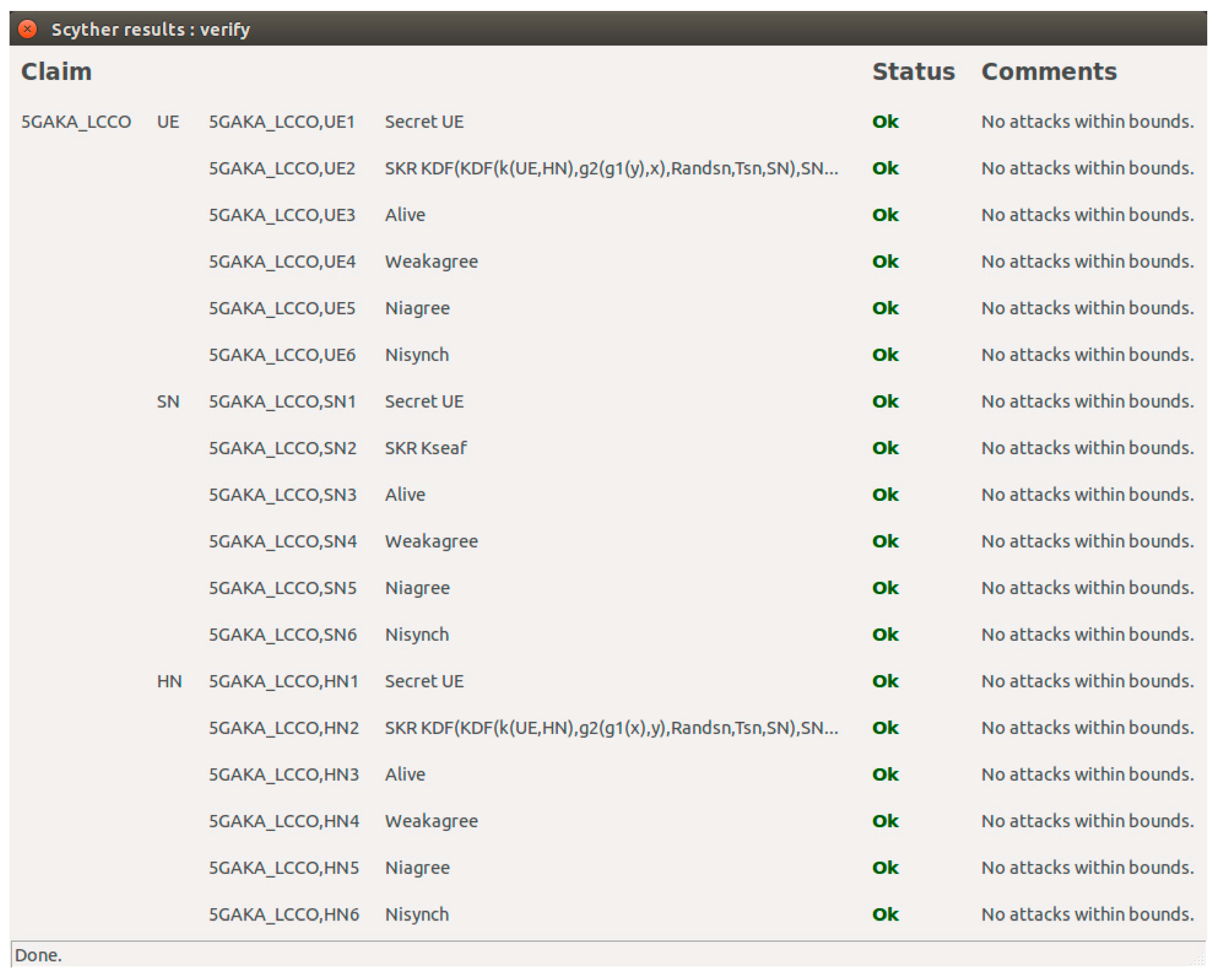
Information | Free Full-Text | 5GAKA-LCCO: A Secure 5G Authentication and Key Agreement Protocol with Less Communication and Computation Overhead

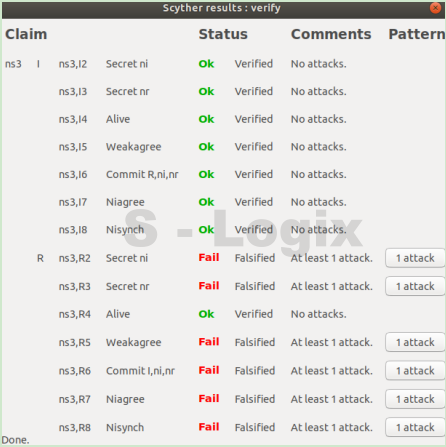
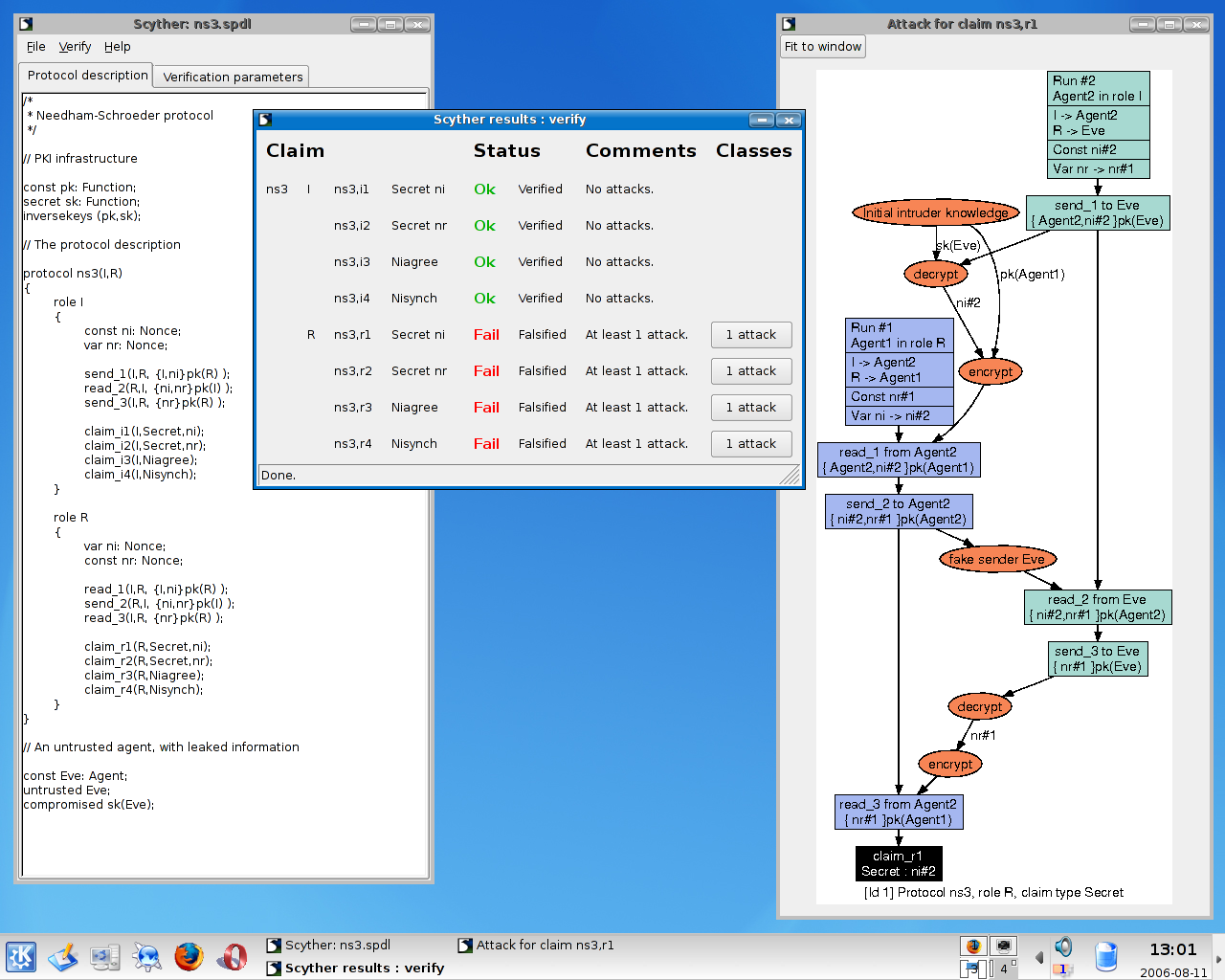
PDF) Analysis and Verification of a Key Agreement Protocol over Cloud Computing Using Scyther Tool | Hazem A . Elbaz - Academia.edu

Information | Free Full-Text | Fuzzy Extractor and Elliptic Curve Based Efficient User Authentication Protocol for Wireless Sensor Networks and Internet of Things